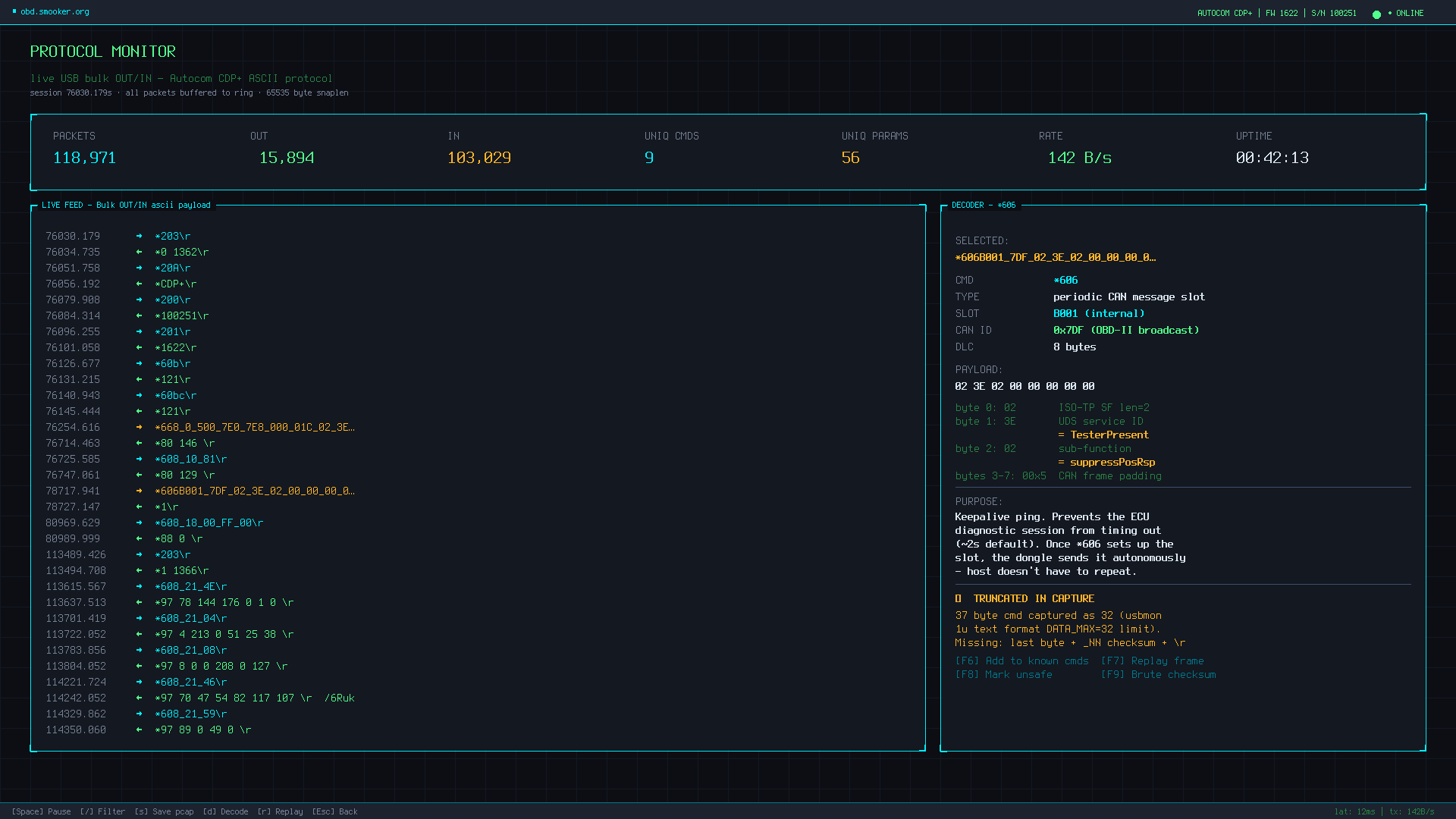
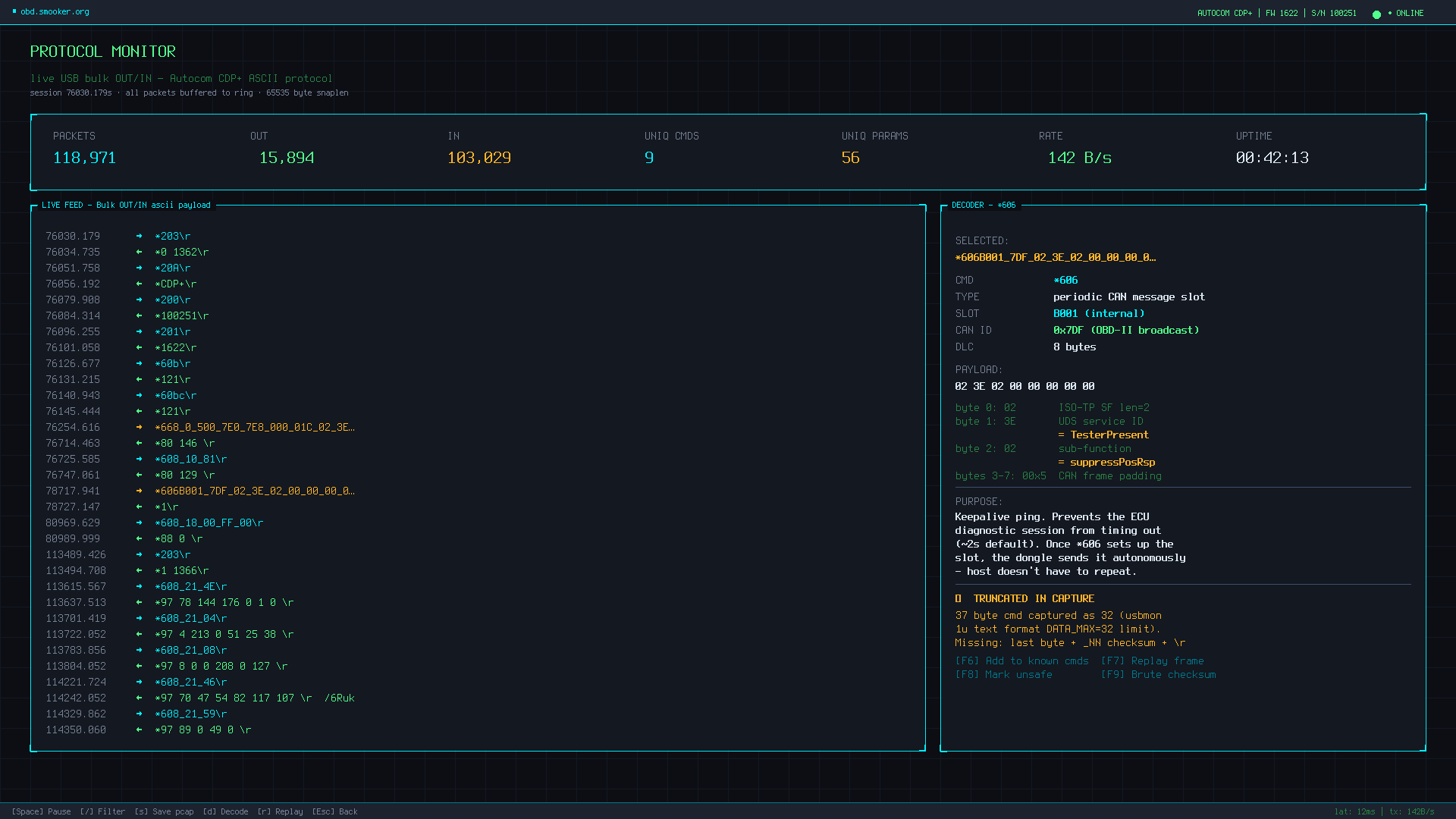
A small open-source toolkit for sniffing, decoding and (eventually) replaying
the proprietary text-based protocol used by the popular Autocom CDP+
diagnostic dongle (also sold as Delphi DS150E and many clones, USB ID
0403:d6da). The internal STM32 talks a custom *cmd_args\r
ASCII protocol over an FTDI bulk pipe — fully readable, no obfuscation, but
until now nobody had publicly documented it for Linux.
| file | purpose |
|---|---|
sniff.c | 200-line C/libpcap USB sniffer, full payload, optional pcap output |
sniff_full.py | Python alternative — binary usbmon, no libpcap dependency |
autocom_sniff.sh | bash quick-look — text-mode usbmon (32-byte truncated, see below) |
decode.py | parses usbmon text dump into readable →/← format |
ANALYSE.md | full protocol analysis: commands, responses, ECU param map |
gen_report.py | pslib-based diagnostic PDF report generator |
*<cmd>[_<arg>[_<arg>…]]\r host → dongle *<resp>[ <data>…]\r dongle → host
Start byte *, terminator \r, fields separated
by _. The dongle wraps CAN frames (and other low-level protocol
frames) inside this text envelope.
| cmd | meaning |
|---|---|
*200 / *201 / *20A | get serial / firmware / device name (returns 100251 / 1622 / CDP+) |
*203 | battery voltage in mV/10 (e.g. *1 1366 = 13.66 V) |
*60b / *60bc | init handshake |
*668_<bus>_<rate>_<txid>_<rxid>_… | configure CAN bus (500 kbps, 7E0/7E8 OBD-II) |
*606<slot>_<canid>_<8 bytes>_<chk>\r | periodic CAN slot (UDS Tester Present keepalive) |
*608_21_<XX> | read ECU parameter at index XX |
*97 XX <bytes> | response to *608_21_XX |
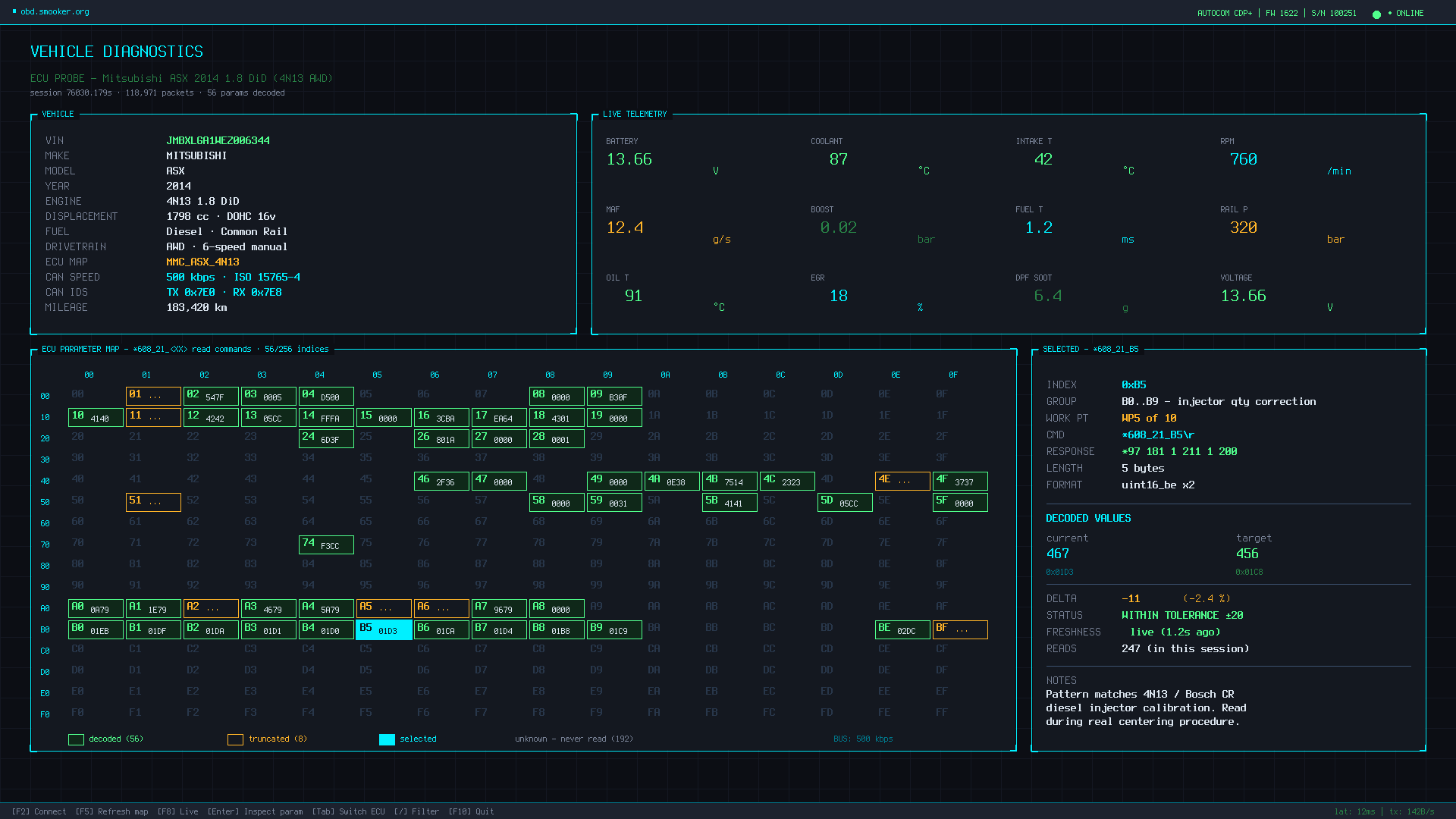
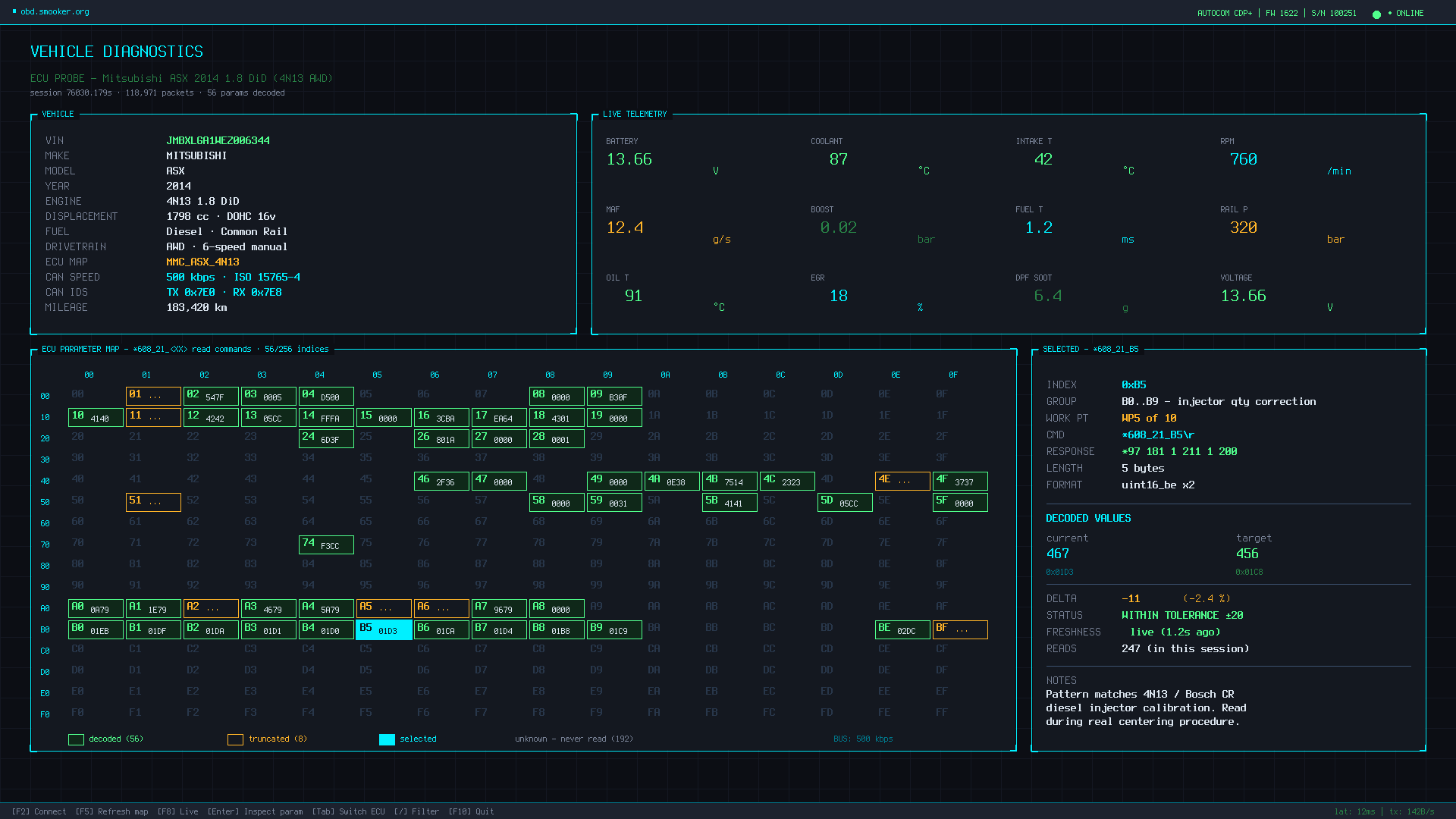
The first capture was made on a 2014 Mitsubishi ASX with the 4N13 1.8-litre diesel, during an injector centering operation in the original Windows software (running inside a Linux KVM with USB passthrough). 119,000 USB packets in ~12 minutes.
56 unique ECU parameter indices were polled by the "read all parameters" function in 5–6 seconds, giving us a near-complete view of the live data set this ECU exposes.
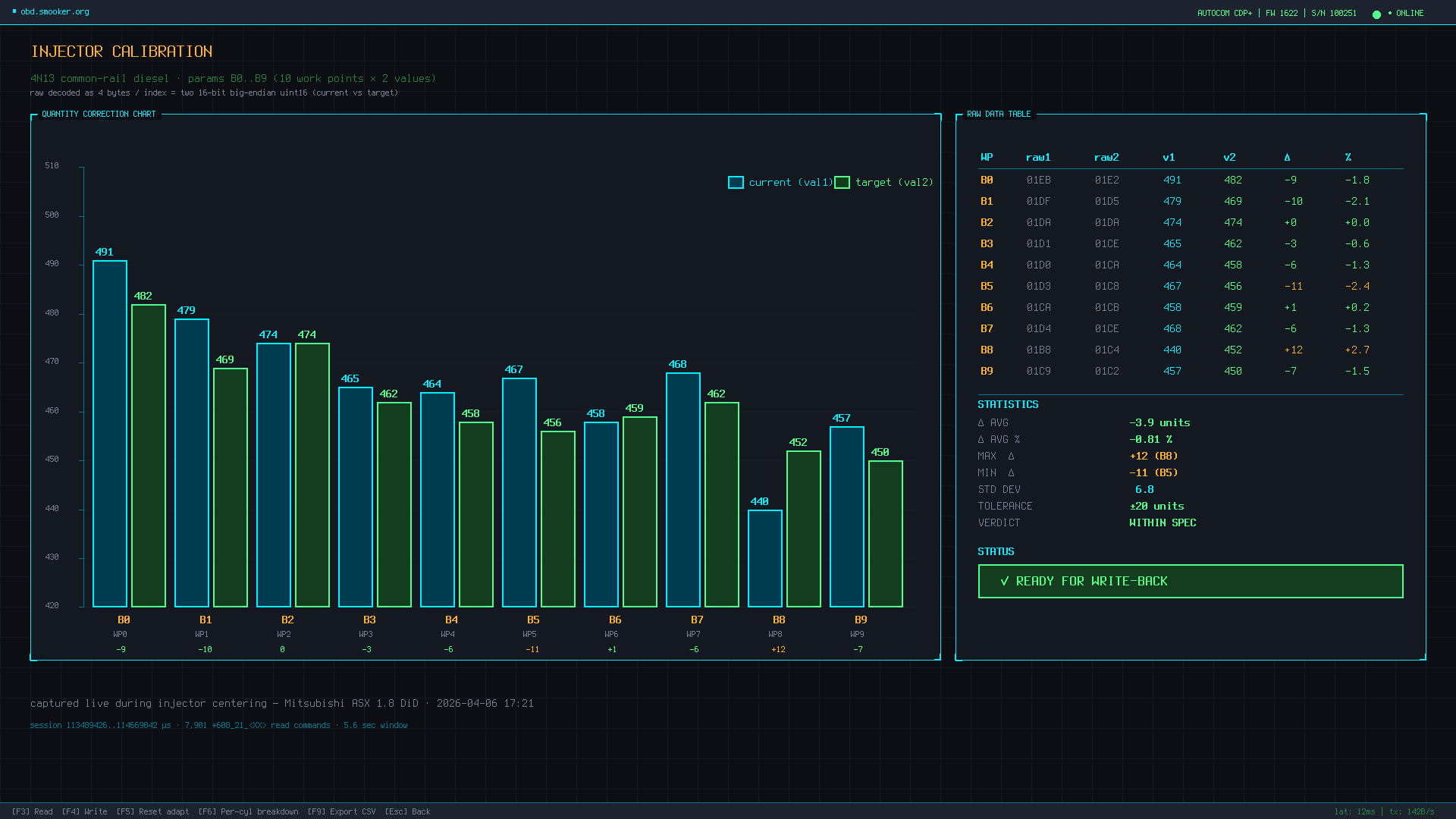
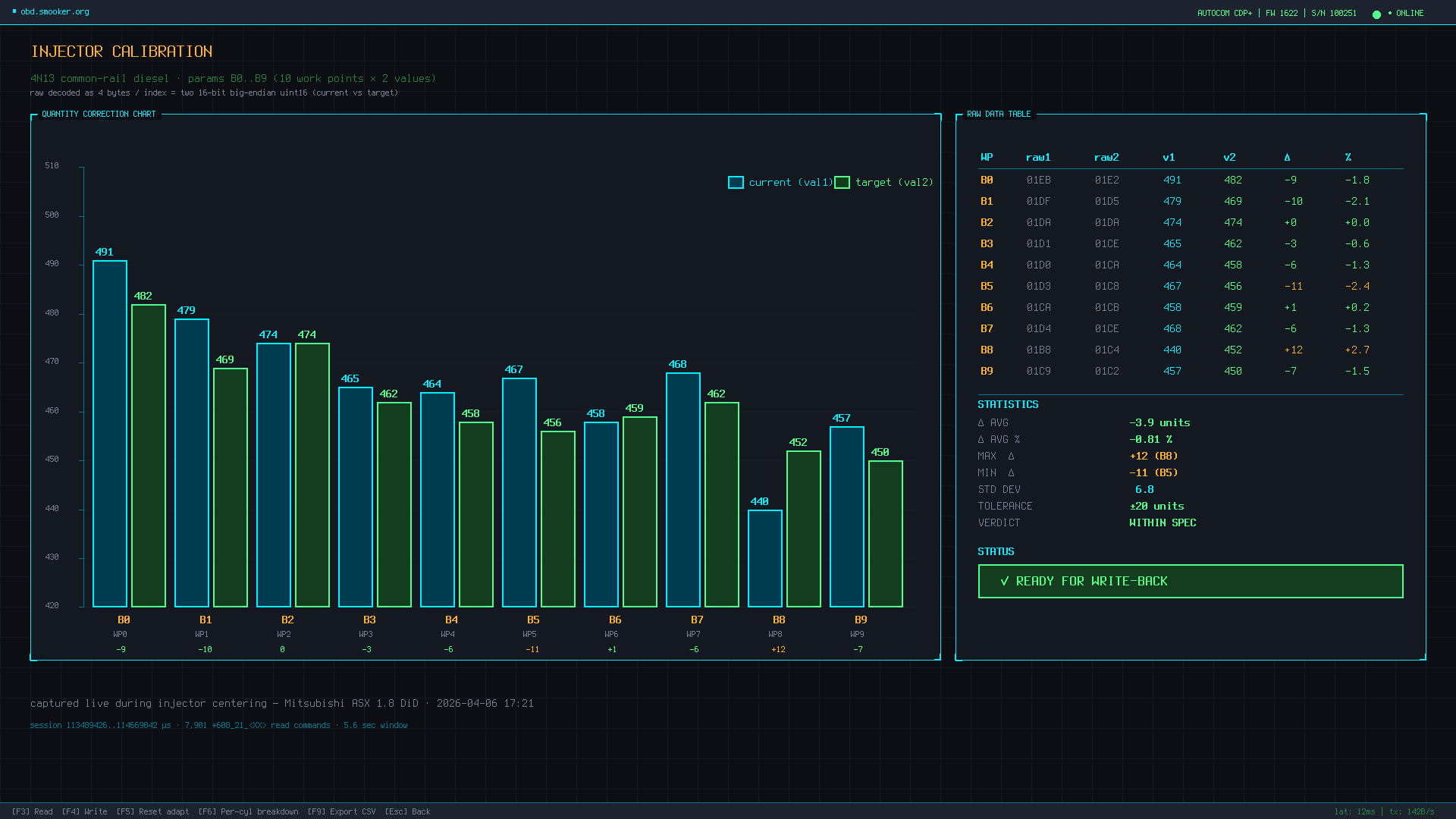
Ten parameters in the 0xB0–0xB9 range, each returning a 4-byte
field decoded as two 16-bit big-endian values. Pattern, value range and
timing all match a textbook injector quantity correction table
(10 work points × 2 values, current vs target). Captured live during a real
centering procedure.
| WP | raw bytes | val 1 | val 2 | Δ |
|---|---|---|---|---|
| B0 | 01EB 01E2 | 491 | 482 | −9 |
| B1 | 01DF 01D5 | 479 | 469 | −10 |
| B2 | 01DA 01DA | 474 | 474 | 0 |
| B3 | 01D1 01CE | 465 | 462 | −3 |
| B4 | 01D0 01CA | 464 | 458 | −6 |
| B5 | 01D3 01C8 | 467 | 456 | −11 |
| B6 | 01CA 01CB | 458 | 459 | +1 |
| B7 | 01D4 01CE | 468 | 462 | −6 |
| B8 | 01B8 01C4 | 440 | 452 | +12 |
| B9 | 01C9 01C2 | 457 | 450 | −7 |
Reverse engineering for interoperability and educational purposes (EU Software Directive 2009/24/EC Art. 6). Not affiliated with Autocom, Delphi or any OEM. The CDP+ dongle uses internal relays to switch between automotive protocols and power lines — wrong commands can pull pins to 12 V where they shouldn't be and damage the dongle, OBD connector or ECU. Replay only byte-perfect captured sequences. Use at your own risk.